filmov
tv
Cloud Security and Zero Trust, Part 1: Software Defined Perimeter to ZT

Показать описание
Six years ago, the world was talking about software defined perimeter (SDP) as an architecture. Now, everyone’s talking about Zero Trust as a security philosophy, but the core principles remain the same. Understand where CSA started and where we are now when it comes to software defined perimeter (SDP) and Zero Trust.
In the first video of this three-part series, Jason Garbis, Principal at Numberline Security and Co-Chair of the ZT Working Group at CSA, recaps the progress over the last 6 years and the current work that CSA is doing to promote Zero Trust best practices.
Further References:
Follow us to gain the latest cloud security insights:
#cloudsecurity #zerotrust
In the first video of this three-part series, Jason Garbis, Principal at Numberline Security and Co-Chair of the ZT Working Group at CSA, recaps the progress over the last 6 years and the current work that CSA is doing to promote Zero Trust best practices.
Further References:
Follow us to gain the latest cloud security insights:
#cloudsecurity #zerotrust
Zero Trust Explained in 4 mins
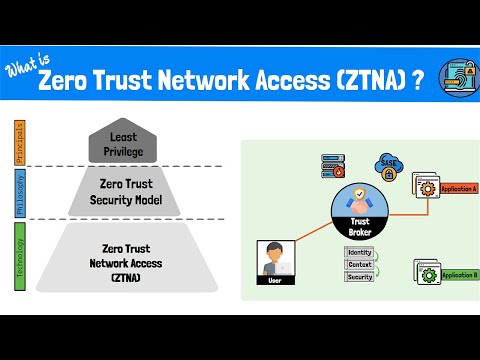
What is Zero Trust Network Access (ZTNA)? The Zero Trust Model, Framework and Technologies Explained
Zero Trust in 5 Minutes with Brian Deitch
How to design and setup a Zero-Trust Cloud Security Architecture?
Prisma Lightboard - Zero Trust Cloud Security
Cybersecurity and Zero Trust
Duo Security: Cloud Based Zero Trust Security
Cloud Security and Zero Trust, Part 1: Software Defined Perimeter to ZT
Saturday Security: Fortinet Shuts Down a Data Breach and Extortion Attempt
Using Zero Trust security for the hybrid cloud
How Zero Trust Security Works
Zero Trust Explained
Cloud Security Architecture - Zero Trust Model
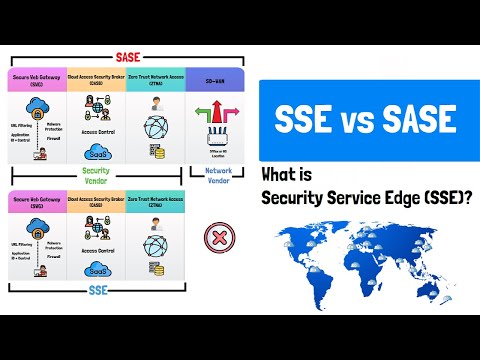
What is Security Service Edge (SSE)? SASE vs SSE vs VPN
Zero Trust Network Access (ZTNA) - Cloud Security Solutions from Lookout
Simplified Google Cloud network security: Zero-trust and beyond
What is Zero Trust Security?
What's new in zero trust
What is Zero Trust Architecture?
Data Security and Protection with Zero Trust
Forcepoint Cloud Security Game Plan | 1 - Building an Adaptive Zero Trust Architecture
Understanding and Getting Started with ZERO TRUST
Cloud Security and Zero Trust, Part 3: Starting your Zero Trust Journey
AWS Summit DC 2022 - Integrating AWS services and Zero Trust networks
Комментарии
 0:03:43
0:03:43
 0:07:44
0:07:44
 0:04:39
0:04:39
 0:04:01
0:04:01
 0:03:46
0:03:46
 0:17:59
0:17:59
 0:00:16
0:00:16
 0:05:26
0:05:26
 0:00:59
0:00:59
 0:18:08
0:18:08
 0:04:38
0:04:38
 0:02:12
0:02:12
 0:09:02
0:09:02
 0:06:36
0:06:36
 0:01:38
0:01:38
 0:45:07
0:45:07
 0:01:30
0:01:30
 0:15:15
0:15:15
 0:00:13
0:00:13
 0:02:51
0:02:51
 0:05:01
0:05:01
 0:57:11
0:57:11
 0:10:39
0:10:39
 0:46:29
0:46:29