filmov
tv
DMZ Explained | Demilitarised Zone

Показать описание
Join the Discord Server!
---------------------
MY FULL CCNA COURSE
FREE CCNA FLASHCARDS
HOW TO PASS THE CCNA
SOCIAL
Disclaimer: These are affiliate links. If you purchase using these links, I'll receive a small commission at no extra charge to you.
---------------------------------------------------------------------------------------------------------------
What is a DMZ?
Well, the name comes from the military.
In military terms, it's an area where military activity is forbidden, often along borders. A well-known example of a Demilitarised Zone is the border between North and South Korea.
A DMZ, in computer terms, is similar. It's an area of a network where security rules and policies are more relaxed.
But, why on earth would you want to relax security policies?
Well, imagine you have a web server. You install it in your network just like all of your other devices.
You want people to access your web server and visit your website right? So you allow public access to your web server through your router and firewall.
Now, this may seem fine, but it leaves you vulnerable to attacks. Web servers and websites are not bulletproof, and they require a lot of work to keep maintained, up-to-date and secure.
Let's say an attacker targets your website, and that attacker can get access to the web server itself. This is where the problems start.
Because our web server is installed alongside our other corporate servers and workstations, the attacker can now start to attack these machines from the web server. With a bit of luck, the attacker could gain access to the entire network. This is called lateral movement.
From here, it's really up to the attacker what they do next. It could be the exfiltration of your data or infecting your systems with ransomware, which will encrypt your data.
So, what is the solution?
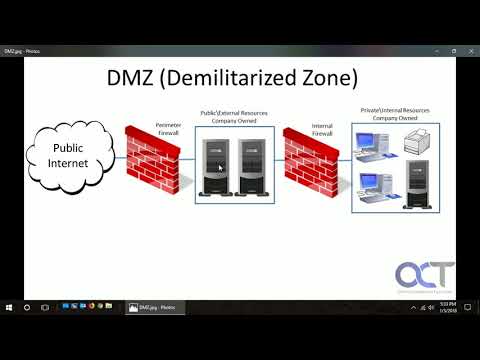
Instead of installing the web server in the corporate network, we can install it into its own network called a DMZ.
A DMZ is created with two firewalls. The first firewall allows public access to our web server; the second firewall blocks public access.
If an attacker can access our web server, they may try to get lateral movement by attacking other machines in the network. Well, because we have separated this web server into its own network, there are no other machines to attack, and our second firewall blocks access to our corporate network.
So, while the web server has been compromised, the DMZ allows us to contain the attack to just that web server.
This dramatically reduces the cyber attack's impact and makes the hacker sad. Meanwhile, the rest of the corporate network is unharmed and operating as normal.
---------------------
MY FULL CCNA COURSE
FREE CCNA FLASHCARDS
HOW TO PASS THE CCNA
SOCIAL
Disclaimer: These are affiliate links. If you purchase using these links, I'll receive a small commission at no extra charge to you.
---------------------------------------------------------------------------------------------------------------
What is a DMZ?
Well, the name comes from the military.
In military terms, it's an area where military activity is forbidden, often along borders. A well-known example of a Demilitarised Zone is the border between North and South Korea.
A DMZ, in computer terms, is similar. It's an area of a network where security rules and policies are more relaxed.
But, why on earth would you want to relax security policies?
Well, imagine you have a web server. You install it in your network just like all of your other devices.
You want people to access your web server and visit your website right? So you allow public access to your web server through your router and firewall.
Now, this may seem fine, but it leaves you vulnerable to attacks. Web servers and websites are not bulletproof, and they require a lot of work to keep maintained, up-to-date and secure.
Let's say an attacker targets your website, and that attacker can get access to the web server itself. This is where the problems start.
Because our web server is installed alongside our other corporate servers and workstations, the attacker can now start to attack these machines from the web server. With a bit of luck, the attacker could gain access to the entire network. This is called lateral movement.
From here, it's really up to the attacker what they do next. It could be the exfiltration of your data or infecting your systems with ransomware, which will encrypt your data.
So, what is the solution?
Instead of installing the web server in the corporate network, we can install it into its own network called a DMZ.
A DMZ is created with two firewalls. The first firewall allows public access to our web server; the second firewall blocks public access.
If an attacker can access our web server, they may try to get lateral movement by attacking other machines in the network. Well, because we have separated this web server into its own network, there are no other machines to attack, and our second firewall blocks access to our corporate network.
So, while the web server has been compromised, the DMZ allows us to contain the attack to just that web server.
This dramatically reduces the cyber attack's impact and makes the hacker sad. Meanwhile, the rest of the corporate network is unharmed and operating as normal.
Комментарии
 0:06:11
0:06:11
 0:06:14
0:06:14
 0:12:32
0:12:32
 0:04:14
0:04:14
 0:01:44
0:01:44
 0:03:56
0:03:56
 0:21:52
0:21:52
 0:10:30
0:10:30
 0:02:42
0:02:42
 0:03:32
0:03:32
 0:01:52
0:01:52
 0:21:47
0:21:47
 0:03:02
0:03:02
 0:00:23
0:00:23
 0:05:57
0:05:57
 0:11:09
0:11:09
 0:01:55
0:01:55
 0:06:26
0:06:26
 0:00:12
0:00:12
 0:16:11
0:16:11
 0:06:15
0:06:15
 0:00:30
0:00:30
 0:01:15
0:01:15
 0:08:11
0:08:11