filmov
tv
802.1X | Network Basics

Показать описание
We're talking about 802.1x - the authentication mechanism we leverage to segment network access control and authentication of devices trying to access the network!
FOLLOW US:
FOLLOW US:
802.1X | Network Basics
Understand how the Dot1X (802.1x) protocol works
MicroNugget: How to Use 802.1X and NAC
IEEE 802.1X | Understanding 802.1X Authentication | What is IEEE 802.1X and How does 802.1X work?
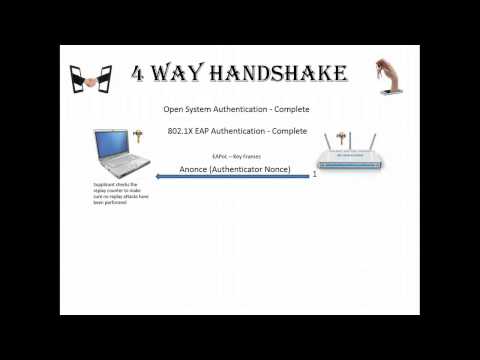
802.1X Authentication and 4-Way Handshake for WiFi Step by Step
Aruba ClearPass Workshop (2021) - Wireless Access #1 - 802.1X WPA-Enterprise - Basic part 1
EAP - Extensible Authentication Protocol
Cisco Tech Talk: How to Use 802.1x EAP Statistics
Aruba ClearPass Workshop - Wireless #1 - Aruba Instant WPA2 Enterprise 802.1X (basic)
Cisco ISE 802 1X Configuration
Port Security and 802.1X - CompTIA Security+ SY0-401: 1.2
Port Security vs Port Based Authentication (802.1x) Whats the Difference?
How to Configure IEEE 802.1X Port-Based Authentication l Step-by-Step Tutorial
Network Access Control with 802.1X - CompTIA Network+ N10-005: 5.3
802.1x and Beyond!
ZoneDirector: Configuring 802.1x Authentication with Radius
NetLAB.si: HowTo configure 802.1x WiFi on MikroTik and Windows radius
802.1X Simplification & Automation with IBNS 2.0
FortiGate/FortiSwitch 802.1x port authentication (and MAB) with Windows RADIUS
Ubiquiti Unifi RADIUS 802.1x Authentication Configuration
Cisco ISE: Wired and Wireless 802.1X Network Authentication | Global Knowledge
RADIUS Authentication Pros and Cons
ExtremeCloud IQ – 802.1X Authentication – Extreme Dojo
Wireless Authentication and Key Generation
Комментарии
 0:04:04
0:04:04
 0:18:05
0:18:05
 0:03:47
0:03:47
 0:07:12
0:07:12
 0:12:53
0:12:53
 0:10:08
0:10:08
 0:07:52
0:07:52
 0:02:37
0:02:37
 0:10:24
0:10:24
 0:25:48
0:25:48
 0:05:33
0:05:33
 0:13:12
0:13:12
 0:14:26
0:14:26
 0:03:50
0:03:50
 0:31:46
0:31:46
 0:08:17
0:08:17
 0:07:54
0:07:54
 0:50:52
0:50:52
 0:17:07
0:17:07
 0:08:52
0:08:52
 0:50:18
0:50:18
 0:02:40
0:02:40
 0:17:31
0:17:31
 0:23:37
0:23:37