filmov
tv
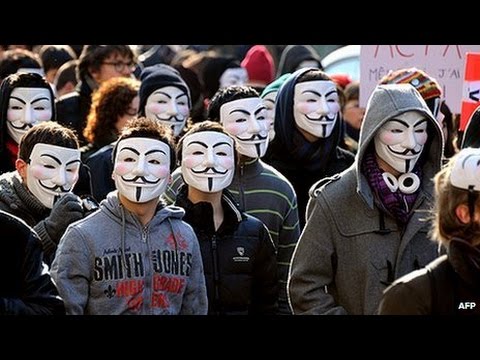
Become Untraceable - How To Create An Anonymous Identity | Tutorial

Показать описание
The Internet is a giant network of privately owned spaces open to public, where every participant knows the exact identity and location of one another and where corporate stalking is a perfectly legitimate business model. If you are not okay with automated decisions being made about your every move, you should consider creating an anonymous identity.
Anonymity is the most powerful mitigation strategy on a publicly observable network such as the Internet. It is the most direct path towards privacy. This guide will tell you exactly what you need to know and do in order to create and maintain your very own anonymous identity.
The Internet is a privacy nightmare because every action is by default identifiable and linkable. That means actions always lead to a unique location and/or account on the network and actions can built a profile over time. Linkability and identifiability are your biggest privacy and anonymity threats on the Internet. For maximum anonymity, both of these threats need to be mitigated to the fullest extent possible.
Our first step with any service will be to dissociate our account details from our personal information. The second step is to compartmentalize our anonymous identities so that they are isolated from our personal identities.
Dissociation and isolation of your anonymous identities are not the only steps to keep your anonymity. Be extremely cautious of what types of data you submit to these services while using them. Always think of the linkability and identifiability threats when using these accounts.
PRIVACY THREAT MODELING
LINDDUN strategy for threat modeling
Linkability
Identifiability
Mitigation strategies
RECOMMENDED TOOLS
KeepassXC
Bitwarden
FIDO security keys
GrapheneOS
Orbot
Tor Browser
Tutanota
ProtonMail
Briar
OnionShare
Wire
Matrix/Element
How to anonymously install applications
Aurora Open Source Software
How to obtain an anonymous burner phone - The Intercept
How to obtain an anonymous burner phone - The Hated One
NEWS SOURCES
Google location tracking
Chainalysis
Credits
Follow me:
The footage and images featured in the video were for critical analysis, commentary and parody, which are protected under the Fair Use laws of the United States Copyright act of 1976.
Комментарии
 0:20:27
0:20:27
 0:11:55
0:11:55
 0:28:59
0:28:59
 0:03:35
0:03:35
 0:10:42
0:10:42
 0:03:15
0:03:15
 0:02:02
0:02:02
 0:02:05
0:02:05
 0:00:57
0:00:57
 0:15:27
0:15:27
 0:05:12
0:05:12
 0:16:08
0:16:08
 0:13:56
0:13:56
 0:17:27
0:17:27
 0:22:31
0:22:31
 0:23:57
0:23:57
 0:15:16
0:15:16
 0:10:01
0:10:01
 0:20:44
0:20:44
 0:03:34
0:03:34
 0:12:21
0:12:21
 0:00:43
0:00:43
 0:14:38
0:14:38
 0:06:49
0:06:49