filmov
tv
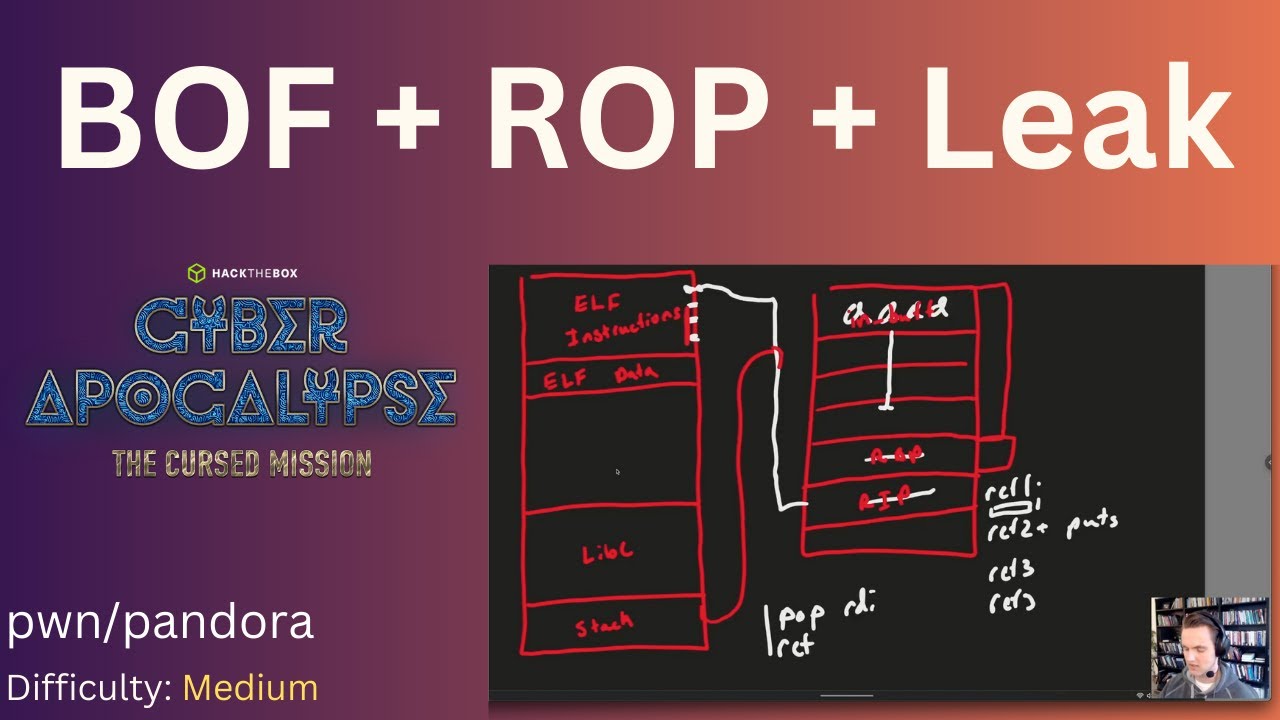
BOF + ROP + libc leak + system('/bin/sh') - Cyber Apocalypse 2023 - pwn/pandora
Показать описание
CTF Writeup Video
00:00 Intro
00:46 Running the binary
01:30 Ghidra
02:11 Checksec
03:18 Whiteboard Solution
11:23 Solve Script
20:40 Flag
00:00 Intro
00:46 Running the binary
01:30 Ghidra
02:11 Checksec
03:18 Whiteboard Solution
11:23 Solve Script
20:40 Flag
BOF + ROP + libc leak + system('/bin/sh') - Cyber Apocalypse 2023 - pwn/pandora
Exploiting Return to Libc (ret2libc) tutorial - pwn109 - PWN101 | TryHackMe
Buffer Overflow Explained | P22 | ROP Chains | CTF Walkthrough
ROP with a very small stack - 32C3CTF teufel (pwnable 200)
Advanced: Introduction to ROP Chains for Binary Exploitation
How-to: libC startup? let's implement argc/v for GCC on DOS!
#7 - Kĩ thuật ROP và ret2libc - pwn07 (Whitehat Wargame 2021)
Return to libc Exploit: Bypass NX bit (Non Executable Stack)
Defeating DEP Using ROP Chains Part 1
14 Ropemporium Ret2win 64bit
Buffer Overflow Explained | P23 | Stack Pivot and Ret2libc | CTF Walkthrough
8 - ROP Emporium Series - ret2csu
CYSE 211 Return to libc lab
CSAW'19 - PWN - Ret2libc w/ PWNTOOLS (baby_boi)
10: Bypassing Stack Canaries (leak + write) - Buffer Overflows - Intro to Binary Exploitation (Pwn)
[FCSC 2021 - Blind Date] Write Up - Blind rop
Bypassing nx in 32 and 64-bit application with ret2libc [AR]
Cyber 442-01 Cyber Operations Return-to-libc attack.
Exploiting Buffer Overflow (BOF) tutorial - pwn101 - PWN101 | TryHackMe
Demonstrationg Buffer Overflow and ASLR Protection P4 | CTF Walkthrough
pwnable.kr - Levels: fd, collision, bof, flag
[Binary exploitation] GOT & PLT internals - Reverse Engineering
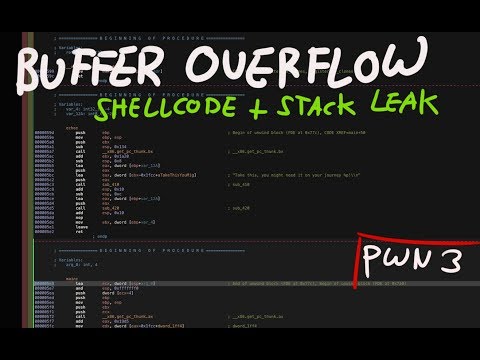
Buffer Overflow - Shellcode + Stack leak address
Format String printf Vulnerabilities (PicoCTF 2022 #46 'flag-leak')
Комментарии
 0:21:09
0:21:09
 0:36:53
0:36:53
 0:13:04
0:13:04
 0:31:39
0:31:39
 1:59:55
1:59:55
 0:07:20
0:07:20
 1:27:49
1:27:49
 0:05:45
0:05:45
 0:13:34
0:13:34
 0:24:02
0:24:02
 0:22:04
0:22:04
 0:34:13
0:34:13
 0:15:22
0:15:22
 0:24:03
0:24:03
 0:14:49
0:14:49
 0:51:04
0:51:04
 1:14:56
1:14:56
 0:23:48
0:23:48
 0:14:53
0:14:53
 0:52:48
0:52:48
 0:21:32
0:21:32
![[Binary exploitation] GOT](https://i.ytimg.com/vi/PVSrbXPAc-Y/hqdefault.jpg) 0:31:01
0:31:01
 0:09:41
0:09:41
 0:19:44
0:19:44