filmov
tv
Demonstrationg Buffer Overflow and ASLR Protection P4 | CTF Walkthrough

Показать описание
Receive Cyber Security Field Notes and Special Training Videos
**********
Patreon
Instagram
Twitter
Facebook
LinkedIn
Website
Backup channel
My Movie channel:
******
**********
Patreon
Website
Backup channel
My Movie channel:
******
Demonstrationg Buffer Overflow and ASLR Protection P4 | CTF Walkthrough
Buffer OverFlow Exploit to open a shell with ASLR enabled | Buffer Overflow | Shellcode | GDB | ASLR
buffer overflow bypass ASLR and DEP with ROP Chain
ARM ASLR bypass Buffer Overflow in Dlink router
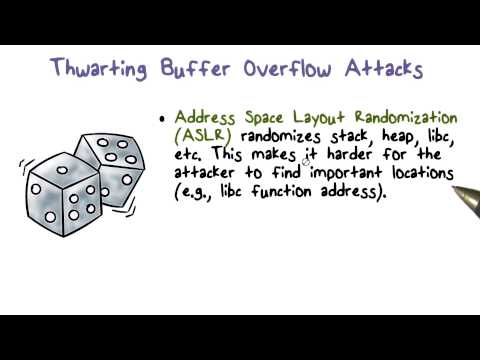
W2_4d - Demonstration of Canaries, W^X, and ASLR to prevent Buffer Overflow Attacks
[pWn - WriteUp] roppity - Buffer overflow bypass aslr / NX
how do hackers exploit buffers that are too small?
Bypassing The Linux Kernel Aslr And Exploiting A Buffer Overflow Vulnerable Application With Ret2Esp
Demo2 - Stack-Based Buffer Overflow Exploit
CS6265 Lab 05 Bypassing DEP and ASLR
Cannot access memory at address // Debugging PIE Binaries affected by ASLR - bin 0x2E
BufferOverflow Linux with ASLR Enabled
03 Bypass ASLR - #Method 1 (JMP ESP)
How to Bypass ASLR using an Information Leak (for Stack Overflow Exploit)
Buffer Overflow Explained | P23 | Stack Pivot and Ret2libc | CTF Walkthrough
ASLR
Cyber Attacks and Defense Lecture 9 - ASLR
OS hacking: Address Space Layout Randomization (ASLR) for shared libraries
Exploit Exercises - Fusion - Level 1 (Remote Exploit/ASLR)
Buffer Overflow Hacking Tutorial (Bypass Passwords)
Exploit Development | Format Strings Series 5/6 - Memory leak + ASLR bypass
OffensiveCon18 - Ilya Smith - Linux ASLR and GNU Libc
Simple X86 Stack Overflow Demonstration [Windows 2000 based]; OSCP Buffer Overflow Demonstration.
34C3 - ASLR on the line
Комментарии
 0:52:48
0:52:48
 0:09:12
0:09:12
 0:01:41
0:01:41
 0:09:35
0:09:35
 0:11:11
0:11:11
![[pWn - WriteUp]](https://i.ytimg.com/vi/Av6hlawPe8Y/hqdefault.jpg) 0:24:31
0:24:31
 0:08:25
0:08:25
 0:06:29
0:06:29
 0:08:23
0:08:23
 0:09:48
0:09:48
 0:13:22
0:13:22
 0:08:25
0:08:25
 0:19:45
0:19:45
 0:13:50
0:13:50
 0:22:04
0:22:04
 0:03:49
0:03:49
 0:37:25
0:37:25
 0:39:23
0:39:23
 0:08:28
0:08:28
 0:55:39
0:55:39
 0:09:28
0:09:28
 0:47:35
0:47:35
 0:05:26
0:05:26
 0:44:14
0:44:14