filmov
tv
Effective Access

Показать описание
This video will look at effective access. Effective access is the access a user has when they access a resource and the permissions for that resource have been evaluated. Knowing the effective access a user has is useful when troubleshooting problems on the network.
Effective Access
00:12 Effective access is essentially the access that a user has when they attempt to access an object. To determine effective access, first the explicit permissions are looked at. If the user is not given access via the explicit permissions, next the inherited permissions are looked at. If these allow access, the user will be given access. The process becomes more complicated in large organizations where there may be 100’s or 1000’s of groups. When groups are nested together this becomes more difficulty. Being able to quickly determine what permissions a user has with effective access will assist the administrator with troubleshooting. Effective Access00:59 To determine the effective access a user has, a few things should be remembered. First, allow permissions are cumulative. For example, if the user has read access and write access, these permissions are combined together so the user has read and write. The deny permission will however overwrite any other permission. There however is one exception to this. If the deny permission is used in inherited permissions and explicit permissions are also configured, the explicit permission will override the deny permission.
Demonstration
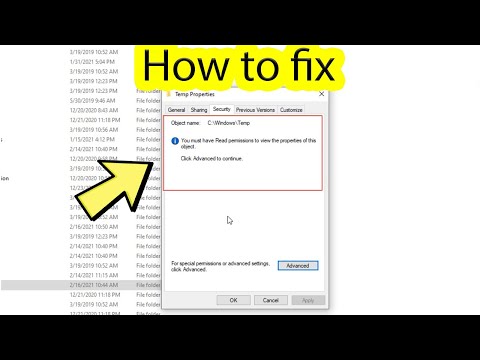
01:58 Open Windows Explorer. 02:10 Open the properties for the sales folder by right clicking it and selecting properties. 02:18 Once the properties for the folder have been opened, select the security tab. In this example, there are 3 different groups that have been added to the security tab. In a large company there may be more than this. In order for the administrator to determine if a user has access, they would need to go through each group and see if the user is a member of that group. 02:46 To see the effective access for a user, press the button advanced and then from advanced security settings select the tab Effective Access. 02:58 To test a user’s access, select the option select a user and then enter in the user that you want to test. 03:10 You also have the option Select a device if you want to check what access a device has. 03:19 The effective access tab also includes the ability to check for user and device claims if you have federation services setup on your network. 03:23 Once the options that you want to test have been configured, press the button View effective access. The access will be shown below. In this example John Doe does not have the permission Delete subfolders and files. Some applications require this permission to save files as they need to delete files when saving data.
04:08 In some cases, to fix access you may need to add additional groups. Before you do this, you have the option at the top Add items which will allow additional groups to be added. In this case the sales manager group was added. Once items have been added, press the button view effective access and the list of permissions will be updated. The administrator is then able to see if adding the items has fixed the permissions problems.
References Installing and Configuring Windows Server 2012 R2 Exam Ref 70-410 pg 80-81
Effective Access
00:12 Effective access is essentially the access that a user has when they attempt to access an object. To determine effective access, first the explicit permissions are looked at. If the user is not given access via the explicit permissions, next the inherited permissions are looked at. If these allow access, the user will be given access. The process becomes more complicated in large organizations where there may be 100’s or 1000’s of groups. When groups are nested together this becomes more difficulty. Being able to quickly determine what permissions a user has with effective access will assist the administrator with troubleshooting. Effective Access00:59 To determine the effective access a user has, a few things should be remembered. First, allow permissions are cumulative. For example, if the user has read access and write access, these permissions are combined together so the user has read and write. The deny permission will however overwrite any other permission. There however is one exception to this. If the deny permission is used in inherited permissions and explicit permissions are also configured, the explicit permission will override the deny permission.
Demonstration
01:58 Open Windows Explorer. 02:10 Open the properties for the sales folder by right clicking it and selecting properties. 02:18 Once the properties for the folder have been opened, select the security tab. In this example, there are 3 different groups that have been added to the security tab. In a large company there may be more than this. In order for the administrator to determine if a user has access, they would need to go through each group and see if the user is a member of that group. 02:46 To see the effective access for a user, press the button advanced and then from advanced security settings select the tab Effective Access. 02:58 To test a user’s access, select the option select a user and then enter in the user that you want to test. 03:10 You also have the option Select a device if you want to check what access a device has. 03:19 The effective access tab also includes the ability to check for user and device claims if you have federation services setup on your network. 03:23 Once the options that you want to test have been configured, press the button View effective access. The access will be shown below. In this example John Doe does not have the permission Delete subfolders and files. Some applications require this permission to save files as they need to delete files when saving data.
04:08 In some cases, to fix access you may need to add additional groups. Before you do this, you have the option at the top Add items which will allow additional groups to be added. In this case the sales manager group was added. Once items have been added, press the button view effective access and the list of permissions will be updated. The administrator is then able to see if adding the items has fixed the permissions problems.
References Installing and Configuring Windows Server 2012 R2 Exam Ref 70-410 pg 80-81
Комментарии
 0:05:12
0:05:12
 0:03:17
0:03:17
 0:02:50
0:02:50
 0:05:43
0:05:43
 0:02:28
0:02:28
 0:13:08
0:13:08
 0:11:13
0:11:13
 0:03:09
0:03:09
 0:00:57
0:00:57
 0:07:13
0:07:13
 0:10:29
0:10:29
 0:01:36
0:01:36
 0:06:12
0:06:12
 0:03:01
0:03:01
 0:01:50
0:01:50
 0:17:48
0:17:48
 0:14:23
0:14:23
 0:01:23
0:01:23
 0:01:35
0:01:35
 0:02:02
0:02:02
 0:00:31
0:00:31
 0:02:14
0:02:14
 0:07:26
0:07:26
 0:03:35
0:03:35