filmov
tv
Symmetric Key Encryption | Symmetric Key Cryptography

Показать описание
This lecture talks about Symmetric Key Encryption or you can also say symmetric Key Cryptography in the Subject Cryptography and System Security or Cryptography and Network Security in Hindi.
Purchase notes right now,
more details below:
Cryptography and System Security Playlist:
System Programming & Compiler Construction Playlist:
*Mobile Computing Playlist:
*Digital Signal & Image Processing Playlist:
* Artificial Intelligence:
*Gears used for this YouTube Channel:
*Let's connect:
Purchase notes right now,
more details below:
Cryptography and System Security Playlist:
System Programming & Compiler Construction Playlist:
*Mobile Computing Playlist:
*Digital Signal & Image Processing Playlist:
* Artificial Intelligence:
*Gears used for this YouTube Channel:
*Let's connect:
Symmetric Key and Public Key Encryption
Symmetric Key Encryption and Data Authentication
Private Key Encryption (Symmetric Key Encryption)
Asymmetric Encryption - Simply explained
Encryption - Symmetric Encryption vs Asymmetric Encryption - Cryptography - Practical TLS
Symmetric Key Cryptography | Stream Cipher & Block Cipher Explained | Network Security | Simplil...
Symmetric vs. Asymmetric Encryption - CompTIA Security+ SY0-401: 6.1
Lec-81: Symmetric Key Cryptography in Network Security with examples
RSA encrypt, decrypt, and digital signatures with PyCryptoDome
Symmetric Key Encryption Examples
Symmetric Encryption Demo
How To: Symmetric Key Encryption
What is Symmetric Encryption? Simply Explained | Venafi Chalk Talk
How Does Symmetric Encryption Work?
Public Key Cryptography - Computerphile
Symmetric Cryptosystems - Applied Cryptography
Symmetric Key Cryptography (CISSP Free by Skillset.com)
Symmetric and Asymmetric Cryptography - SY0-601 CompTIA Security+ : 2.8
DiSE: Distributed Symmetric-key Encryption
What is symmetric encryption?
What Is Symmetric Encryption?
Symmetric Encryption Algorithms
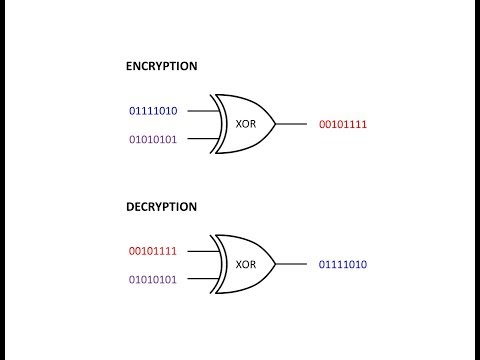
Symmetric Key Cryptography: The XOR Cipher
Symmetric and Asymmetric Key Cryptography
Комментарии
 0:06:45
0:06:45
 0:04:07
0:04:07
 0:04:52
0:04:52
 0:04:40
0:04:40
 0:13:58
0:13:58
 0:10:41
0:10:41
 0:04:18
0:04:18
 0:06:14
0:06:14
 1:13:38
1:13:38
 0:07:25
0:07:25
 0:04:31
0:04:31
 0:05:22
0:05:22
 0:01:45
0:01:45
 0:02:03
0:02:03
 0:06:20
0:06:20
 0:02:27
0:02:27
 0:06:08
0:06:08
 0:09:21
0:09:21
 0:23:30
0:23:30
 0:04:49
0:04:49
 0:00:44
0:00:44
 0:04:56
0:04:56
 0:07:46
0:07:46
 0:03:35
0:03:35