filmov
tv
Analyzing a Compromised Windows With Windows Event Logs | CTF Walkthrough

Показать описание
In this video walk-through, we covered the Event Horizon challenge from hackthebox where we analyzed windows event logs to reveal powershell remote system commands.
**********
Receive Cyber Security Field Notes and Special Training Videos
*******
Instagram
Twitter
Facebook
LinkedIn
Website
Patreon
Backup channel
My Movie channel:
**********
Receive Cyber Security Field Notes and Special Training Videos
*******
Website
Patreon
Backup channel
My Movie channel:
Analyzing a Compromised Windows With Windows Event Logs | CTF Walkthrough
How to tell if your PC is Hacked? Process Forensics
How to know if your PC is hacked? Suspicious Network Activity 101
Is your PC hacked? RAM Forensics with Volatility
How you get Hacked: what attackers use today
How to know if your PC is hacked? Digital Forensics 101
Windows Secure Boot Compromised! What You Need to Know by a Retired Microsoft Engineer
The Malware that hacked Linus Tech Tips
Malware beats Windows Defender: How you get hacked
Cybersecurity Expert Demonstrates How Hackers Easily Gain Access To Sensitive Information
How to Check if your PC is Hacked
Investigating A Hacked Windows with Powershell | TryHackMe Investigating Windows 3.X
Analyzing a Hacked WebServer With Wireshark | CTF Walkthrough
How you get hacked: Undetected Malware
Windows 11 HACKED: Critical Vulnerability Explained [CVE-2024-38063]
This Is How I HACKED Windows!
IPv6 keeps getting hacked on Windows
3 signs to Check if your Computer's HACKED [SPY SOFTWARE]
Analysing A Hacked System
Detect and respond to compromise in Microsoft Defender for Office 365
Ever wondered if your PC has been hacked? Part 7
How to tell if your Wifi is hacked?
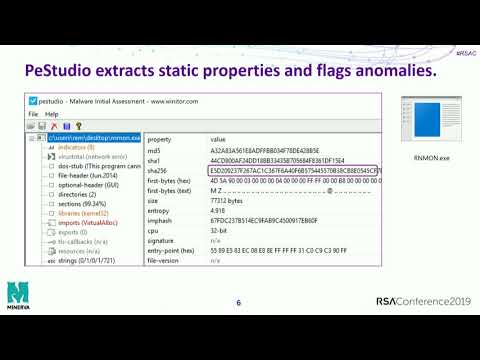
Practical Malware Analysis Essentials for Incident Responders
Bad USB compromised Windows 7 machine | Rubber Ducky | ATtinny85 | Metasploit #shorts
Комментарии
 0:10:41
0:10:41
 0:08:57
0:08:57
 0:10:19
0:10:19
 0:14:29
0:14:29
 0:09:02
0:09:02
 0:11:01
0:11:01
 0:09:36
0:09:36
 0:10:13
0:10:13
 0:07:26
0:07:26
 0:03:27
0:03:27
 0:19:44
0:19:44
 0:45:12
0:45:12
 0:14:37
0:14:37
 0:10:01
0:10:01
 0:00:37
0:00:37
 0:11:55
0:11:55
 0:14:40
0:14:40
 0:05:34
0:05:34
 0:45:18
0:45:18
 0:05:13
0:05:13
 0:00:13
0:00:13
 0:09:27
0:09:27
 0:50:49
0:50:49
 0:00:30
0:00:30