filmov
tv
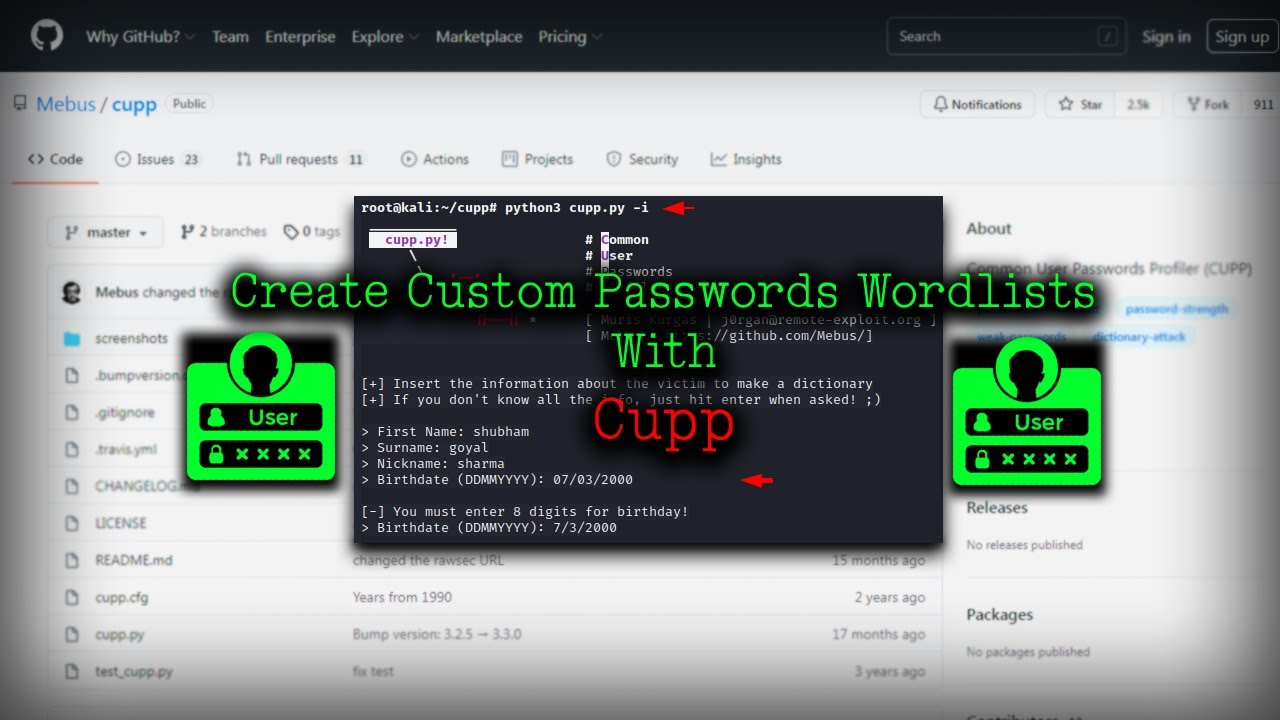
How Hackers can guess your passwords – Common User Passwords Profiler | Kali Linux |
Показать описание
Usernames and Password values are the most commonly used methods for authentication purposes in almost every web application or any type of application. When the credentials provided in this type match the values stored at the server, only the user is authenticated to the specified service. Using weak Usernames and Passwords may lead to various impactful cyber threats like Password Cracking, Brute-Forcing, and Account Takeover. CUPP tool is an automated script written in the python language that interacts with the user and answers some fundamental questions about the victim like Name, Company Name, Partner’s Name, etc. After analyzing these answers, the CUPP tool generates some possible Usernames+Password words that attackers can use for various attacks like Password Cracking and Brute-Forcing.
Commands :
$ apt install cupp
$ cupp -h
Options :
-h this menu
-i Interactive questions for user password profiling
-w Use this option to profile existing dictionary,
or WyD.pl output to make some pwnsauce :)
-l Download huge wordlists from repository
-a Parse default usernames and passwords directly from Alecto DB.
-v Version of the program
- END -
DISCLAIMER :--
All video’s and tutorials are for informational and educational purposes only. We believe that ethical hacking, information security and cyber security should be familiar subjects to anyone using digital information and computers. We believe that it is impossible to defend yourself from hackers without knowing how hacking is done. The tutorials and videos provided on This channel is only for those who are interested to learn about Ethical Hacking, Security, Penetration Testing and malware analysis.Cybersploit is against misuse of the information and we strongly suggest against it. Please regard the word hacking as ethical hacking or penetration testing every time this word is used.
All tutorials and videos have been made using our own routers, servers, websites and other resources, they do not contain any illegal activity. We do not promote, encourage, support or excite any illegal activity or hacking without written permission in general. We want to raise security awareness and inform our readers on how to prevent themselves from being a victim of hackers. If you plan to use the information for illegal purposes, please leave this Video now. We cannot be held responsible for any misuse of the given information.
Commands :
$ apt install cupp
$ cupp -h
Options :
-h this menu
-i Interactive questions for user password profiling
-w Use this option to profile existing dictionary,
or WyD.pl output to make some pwnsauce :)
-l Download huge wordlists from repository
-a Parse default usernames and passwords directly from Alecto DB.
-v Version of the program
- END -
DISCLAIMER :--
All video’s and tutorials are for informational and educational purposes only. We believe that ethical hacking, information security and cyber security should be familiar subjects to anyone using digital information and computers. We believe that it is impossible to defend yourself from hackers without knowing how hacking is done. The tutorials and videos provided on This channel is only for those who are interested to learn about Ethical Hacking, Security, Penetration Testing and malware analysis.Cybersploit is against misuse of the information and we strongly suggest against it. Please regard the word hacking as ethical hacking or penetration testing every time this word is used.
All tutorials and videos have been made using our own routers, servers, websites and other resources, they do not contain any illegal activity. We do not promote, encourage, support or excite any illegal activity or hacking without written permission in general. We want to raise security awareness and inform our readers on how to prevent themselves from being a victim of hackers. If you plan to use the information for illegal purposes, please leave this Video now. We cannot be held responsible for any misuse of the given information.
 0:02:43
0:02:43
 0:00:33
0:00:33
 0:00:05
0:00:05
 0:00:31
0:00:31
 0:03:09
0:03:09
 0:17:53
0:17:53
 0:07:56
0:07:56
 0:06:58
0:06:58
 0:00:43
0:00:43
 0:00:39
0:00:39
 0:08:08
0:08:08
 0:00:53
0:00:53
 0:01:23
0:01:23
 0:02:55
0:02:55
 0:01:57
0:01:57
 0:01:24
0:01:24
 0:00:40
0:00:40
 0:01:51
0:01:51
 0:10:08
0:10:08
 0:08:25
0:08:25
 0:04:18
0:04:18
 0:10:58
0:10:58
 0:11:41
0:11:41
 0:01:08
0:01:08