filmov
tv
1. Critical Authorizations and Critical Combinations Report -RSUSR008_009_NEW - Part 1 of 4

Показать описание
1. Critical Authorizations and Critical Combinations Report -RSUSR008_009_NEW - Part 1 of 4
1. Critical Authorizations and Critical Combinations Report -RSUSR008_009_NEW - Part 1 of 4
How to Find user or Roles with Combination of Critical Authorization?
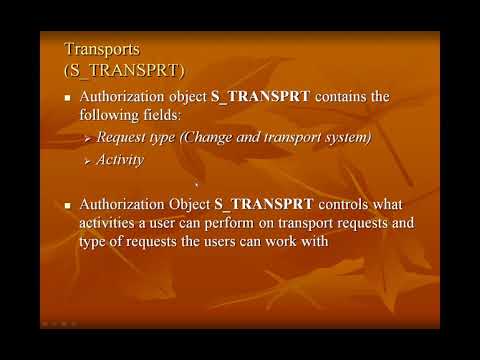
12. Critical Authorization Objects - Part 1
SAP Security - Analyze Critical Authorizations in SAP
3. Critical Authorizations and Critical Combinations Report -RSUSR008_009_NEW - Part 3 of 4
2. Critical Authorizations and Critical Combinations Report -RSUSR008_009_NEW - Part 2 of 4
12. Critical Authorization Objects - Part 18
12. Critical Authorization Objects - Part 16
12. Critical Authorization Objects - Part 2
12. Critical Authorization Objects - Part 11
14 Critical Basis Authorizations
SAP Authorization and Auditing for NetWeaver ||C_AUDSEC_731|| SUIM -Critical Authorizations &T-c...
12. Critical Authorization Objects - Part 3
12. Critical Authorization Objects - Part 20
12. Critical Authorization Objects - Part 5
Sap Architect Critical Basis Authorizations
12. Critical Authorization Objects - Part 12
12. Critical Authorization Objects - Part 10
12. Critical Authorization Objects - Part 6
12. Critical Authorization Objects - Part 19
12. Critical Authorization Objects - Part 13
12. Critical Authorization Objects - Part 4
12. Critical Authorization Objects - Part 9
IAAA - Identification, Authentication, Authorization, and Accountability (Defender Course 01.03)
Комментарии
 0:09:55
0:09:55
 0:01:35
0:01:35
 0:04:49
0:04:49
 0:05:52
0:05:52
 0:21:18
0:21:18
 0:18:55
0:18:55
 0:02:11
0:02:11
 0:07:58
0:07:58
 0:10:27
0:10:27
 0:11:16
0:11:16
 0:06:31
0:06:31
 0:55:06
0:55:06
 0:15:23
0:15:23
 0:05:36
0:05:36
 0:12:29
0:12:29
 0:06:31
0:06:31
 0:12:08
0:12:08
 0:06:40
0:06:40
 0:02:39
0:02:39
 0:07:56
0:07:56
 0:28:10
0:28:10
 0:26:32
0:26:32
 0:10:06
0:10:06
 0:08:31
0:08:31