filmov
tv
R80.10 Unified Access Control policy

Показать описание
This video introduces the R80.10 Unified Access Control policy, and demonstrate the configuration of inline layers.
R80.10 Unified Access Control policy
Start Building Your Unified Policy with R80.10 | Security Management | Tech Bytes
Check Point Certified Security Expert R80.1 Training | Session 4 | Access Control
CPET session 2 - Unified policy R80.10
R80.10 Policy Revision
R80.10 SmartConsole Security Policies View | Threat Prevention
R80.10 Best Practices – Migrating from R77.30
Check Point R80.10 Policy Management – Permissions per layer
Check Point Certified Security Expert R80.1 Training | Session 3 | Unified SmartConsole
Check Point Certified Security Expert R80.1 | Training | Session 1 | Big Picture
R80 Mobile Access - Access Policy with Exceptions
tutorial#20 how to configure checkpoint fw R80.30 application control with inline layer
R80 10 Policy Installation Troubleshooting Part2
Check Point Tech Bytes: R80.20 Identity Tags and Updatable Objects
Managing Security Policy Changes with R80.10 | Tech Bytes
R80 Mobile Access - Clients Based Access Policy
Traffic Handling in the Access Policy: Optimization
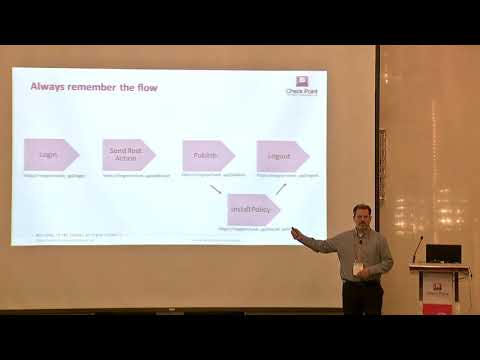
Automating the Rulebase
Check Point R80.10 Policy Management – IPS Protections in Detect (Staging) State
how to configure security policy in check point firewall R80 10
R80.10 Security Management | Tech Bytes: Gateways, Logs, and Manage & Settings
Tutorial: Configuring IPS Settings with R80 Security Management Server | Advanced Threat Prevention
Check Point Certified Security Expert R80.1 Training | Session 5 | Threat Prevention Policy
Check Point Certified Security Expert R80.1 Training Introduction
Комментарии
 0:05:23
0:05:23
 0:05:27
0:05:27
 0:46:24
0:46:24
 0:36:49
0:36:49
 0:04:45
0:04:45
 0:04:47
0:04:47
 0:23:09
0:23:09
 0:02:02
0:02:02
 0:46:37
0:46:37
 0:38:34
0:38:34
 0:02:33
0:02:33
 0:06:35
0:06:35
 0:10:34
0:10:34
 0:07:18
0:07:18
 0:03:13
0:03:13
 0:05:54
0:05:54
 0:05:27
0:05:27
 0:26:26
0:26:26
 0:02:37
0:02:37
 0:01:34
0:01:34
 0:04:32
0:04:32
 0:03:30
0:03:30
 0:30:01
0:30:01
 0:03:59
0:03:59