filmov
tv
Quick setup of SNMP v3 DTLS/TLS access in CentOS/RHEL 7 Linux - net-snmp
Показать описание
The video gives basic overview how to setup SNMP v3 access using DTLS/TLS method.
There are used commands:
_____________
Hello,
in CentOS/RHEL 7 we're going to setup SNMP v3 access
using secure TLS/DTLS access method. We will depend
on self-signed certificates.
For simplicity of this demo there is disabled firewalld and SELinux is in permissive mode.
We will use 2 nodes:
1) Where are we?
cat /etc/centos-release
2) On both nodes install net-snmp RPMs
yum -y install net-snmp net-snmp-libs net-snmp-utils \
net-snmp-agent-libs net-snmp-perl net-snmp-devel
3) Generate self-signed certificate on the agent
net-snmp-cert gencert -I -t snmpd \
4) Generate self-signed certificate on the manager
net-snmp-cert gencert -I -t manager-second \
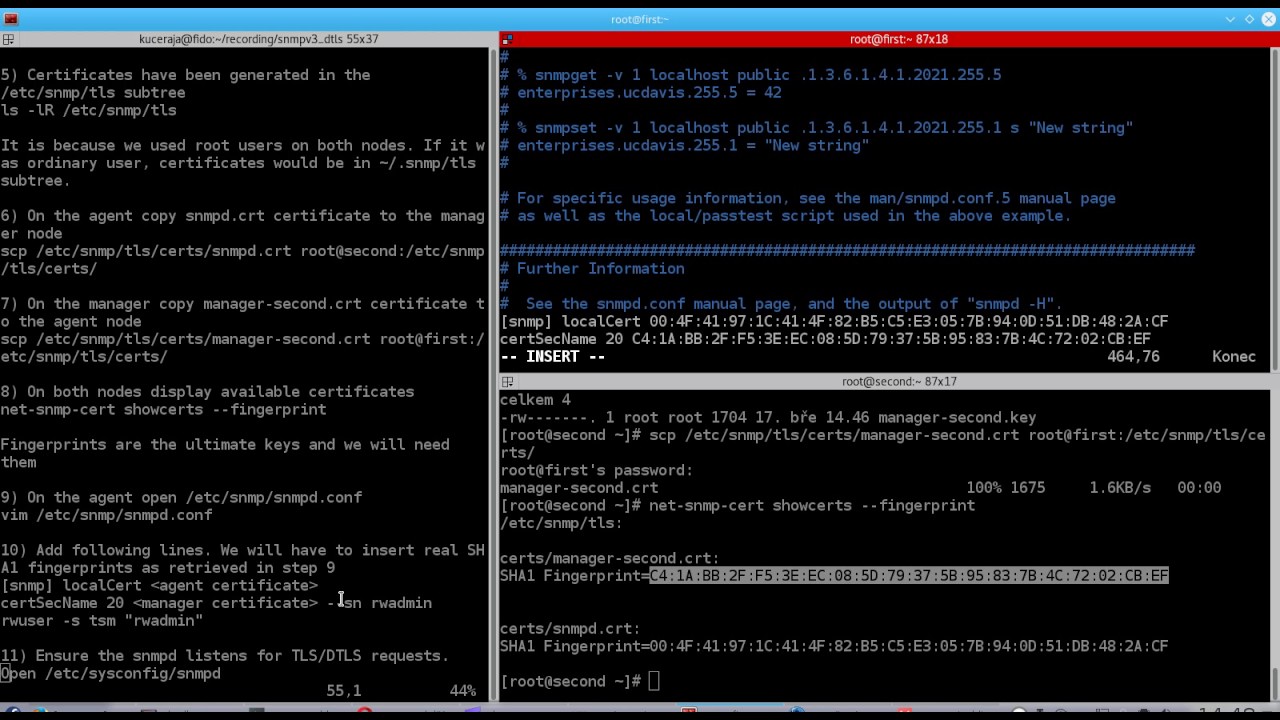
5) Certificates have been generated in the
/etc/snmp/tls subtree
ls -lR /etc/snmp/tls
It is because we used root users on both nodes. If it was ordinary user, certificates would be in ~/.snmp/tls subtree.
8) On both nodes display available certificates
net-snmp-cert showcerts --fingerprint
Fingerprints are the ultimate keys and we will need
them
10) Add following lines. We will have to insert real SHA1 fingerprints as retrieved in step 9
[snmp] localCert {agent certificate}
certSecName 20 {manager certificate} --sn rwadmin
rwuser -s tsm "rwadmin"
11) Ensure the snmpd listens for TLS/DTLS requests.
Open /etc/sysconfig/snmpd
vim /etc/sysconfig/snmpd
12) Add following content
13) Enable snmpd and start it
systemctl enable snmpd
systemctl start snmpd
14) Fetch with following SNMP v3 DTLS request. Again
insert real SHA1 fingerprints as retrieved in step 9
snmpget -v 3 --defSecurityModel=tsm -u manager \
-l authPriv \
-T our_identity={manager certificate} \
-T their_identity={agent certificate} \
dtlsudp:first:10161 sysUpTime.0
It works. Perfect!
15) And finally try let's try TLS variant as well
snmpget -v 3 --defSecurityModel=tsm -u manager \
-l authPriv \
-T our_identity={manager certificate} \
-T their_identity={agent certificate} \
tlstcp:first:10161 sysUpTime.0
Works too. Great!
We've established TLS/DTLS SNMP v3 access to our server.
This is the END. Thank you for watching!
There are used commands:
_____________
Hello,
in CentOS/RHEL 7 we're going to setup SNMP v3 access
using secure TLS/DTLS access method. We will depend
on self-signed certificates.
For simplicity of this demo there is disabled firewalld and SELinux is in permissive mode.
We will use 2 nodes:
1) Where are we?
cat /etc/centos-release
2) On both nodes install net-snmp RPMs
yum -y install net-snmp net-snmp-libs net-snmp-utils \
net-snmp-agent-libs net-snmp-perl net-snmp-devel
3) Generate self-signed certificate on the agent
net-snmp-cert gencert -I -t snmpd \
4) Generate self-signed certificate on the manager
net-snmp-cert gencert -I -t manager-second \
5) Certificates have been generated in the
/etc/snmp/tls subtree
ls -lR /etc/snmp/tls
It is because we used root users on both nodes. If it was ordinary user, certificates would be in ~/.snmp/tls subtree.
8) On both nodes display available certificates
net-snmp-cert showcerts --fingerprint
Fingerprints are the ultimate keys and we will need
them
10) Add following lines. We will have to insert real SHA1 fingerprints as retrieved in step 9
[snmp] localCert {agent certificate}
certSecName 20 {manager certificate} --sn rwadmin
rwuser -s tsm "rwadmin"
11) Ensure the snmpd listens for TLS/DTLS requests.
Open /etc/sysconfig/snmpd
vim /etc/sysconfig/snmpd
12) Add following content
13) Enable snmpd and start it
systemctl enable snmpd
systemctl start snmpd
14) Fetch with following SNMP v3 DTLS request. Again
insert real SHA1 fingerprints as retrieved in step 9
snmpget -v 3 --defSecurityModel=tsm -u manager \
-l authPriv \
-T our_identity={manager certificate} \
-T their_identity={agent certificate} \
dtlsudp:first:10161 sysUpTime.0
It works. Perfect!
15) And finally try let's try TLS variant as well
snmpget -v 3 --defSecurityModel=tsm -u manager \
-l authPriv \
-T our_identity={manager certificate} \
-T their_identity={agent certificate} \
tlstcp:first:10161 sysUpTime.0
Works too. Great!
We've established TLS/DTLS SNMP v3 access to our server.
This is the END. Thank you for watching!
Комментарии
 0:04:14
0:04:14
 0:11:33
0:11:33
 0:08:54
0:08:54
 0:06:56
0:06:56
 0:14:15
0:14:15
 0:10:19
0:10:19
 0:05:50
0:05:50
 0:04:49
0:04:49
 0:18:39
0:18:39
 0:11:44
0:11:44
 0:05:44
0:05:44
 0:05:45
0:05:45
 0:05:57
0:05:57
 0:06:46
0:06:46
 0:11:03
0:11:03
 0:14:25
0:14:25
 0:04:24
0:04:24
 0:10:38
0:10:38
 0:28:11
0:28:11
 0:30:40
0:30:40
 0:01:22
0:01:22
 0:32:27
0:32:27
 0:03:40
0:03:40
 0:30:38
0:30:38