filmov
tv
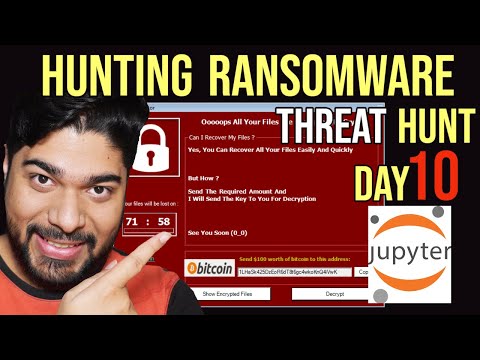
Hunting Ransomware- Jupyter Notebook, Sysmon, Windows Security Log

Показать описание
Human Operated Ransomware (HORA) threat groups are growing in number and strength every day. Today is Day 10 of our Threat Hunting series and, we will will cover the evolution of, tactics inherent to, and threats associated with HORA. We will provide "quick wins" that you can implement now to protect yourself against this ugly threat. We will mainly focus on what to do if ransomware is running *right now*, along with what to do when ransomware has run and the outlook is bleak. We will show what are the best possible ways to hunt for the probable IOA of ransomware attack and how can you document and run your hunt against your network to identify if you are also under attack.
Encrypting all your files is a ransomware actors' final objective. But when the frantic helpdesk calls start coming in, can you quickly identify all impacted devices? Can you determine if data exfil and extortion are part of the attack? Can you tell if they destroyed your backups? This talk will cover common ransomware gang "hands on keyboard" techniques for stealing your data, disabling defenses, and making your data and devices resistant to recovery. Participants will take away hunt logic which can be employed right away for early detection and rapidly scoping a ransomware compromise.
So watch the full episode and leverage the notebook to strategies your hunt technique.
WATCH BELOW Playlists as well, if you want to make your career in DFIR and Security Operations!!
-------------------------------------------------------------------------------------------------------------------------
📞📲
FOLLOW ME EVERYWHERE-
-------------------------------------------------------------------------------------------------------------------------
✔ Twitter: @blackperl_dfir
Encrypting all your files is a ransomware actors' final objective. But when the frantic helpdesk calls start coming in, can you quickly identify all impacted devices? Can you determine if data exfil and extortion are part of the attack? Can you tell if they destroyed your backups? This talk will cover common ransomware gang "hands on keyboard" techniques for stealing your data, disabling defenses, and making your data and devices resistant to recovery. Participants will take away hunt logic which can be employed right away for early detection and rapidly scoping a ransomware compromise.
So watch the full episode and leverage the notebook to strategies your hunt technique.
WATCH BELOW Playlists as well, if you want to make your career in DFIR and Security Operations!!
-------------------------------------------------------------------------------------------------------------------------
📞📲
FOLLOW ME EVERYWHERE-
-------------------------------------------------------------------------------------------------------------------------
✔ Twitter: @blackperl_dfir
Комментарии
 0:24:38
0:24:38
 0:13:42
0:13:42
 1:10:45
1:10:45
 0:11:30
0:11:30
 0:05:35
0:05:35
 0:30:14
0:30:14
 0:00:52
0:00:52
![[21] Malware Lab](https://i.ytimg.com/vi/-7VvMOa1PHg/hqdefault.jpg) 0:04:00
0:04:00
 0:39:05
0:39:05
 0:08:25
0:08:25
 0:10:19
0:10:19
 0:12:24
0:12:24
 0:07:35
0:07:35
 0:13:24
0:13:24
 0:49:46
0:49:46
 0:17:24
0:17:24
 0:59:35
0:59:35
 0:00:31
0:00:31
 1:59:35
1:59:35
 0:01:00
0:01:00
 0:14:48
0:14:48
 0:30:26
0:30:26
 0:59:14
0:59:14
 0:23:00
0:23:00