filmov
tv
Cybersecurity Metrics

Показать описание
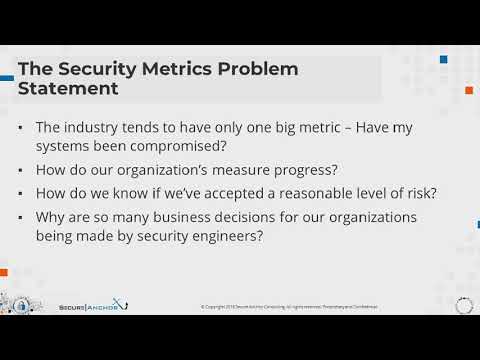
In this episode of Life of a CISO, Dr. Eric Cole delves into the critical challenge of measuring cybersecurity effectiveness, emphasizing the flawed approach many organizations take. He highlights that many companies mistakenly believe that if no visible attacks are detected, their cybersecurity is successful. However, this mentality overlooks the reality that many breaches go unnoticed due to inadequate detection mechanisms. Dr. Cole argues that relying on a lack of detected attacks as a metric for success is both misguided and dangerous, as it often means that companies aren't looking in the right places or using the right metrics to gauge their security posture.
Dr. Cole also explores the systemic issues within organizations that hinder effective cybersecurity. He points out the problematic structure where CISOs report to CIOs, who are primarily focused on availability and uptime, leading to conflicts of interest that compromise security. Dr. Cole advocates for a shift in responsibility and authority, urging companies to recognize that cybersecurity requires independent oversight and clear, measurable metrics that go beyond simply preventing visible attacks. He stresses the need for a fundamental change in how organizations approach cybersecurity, including holding decision-makers accountable for risks and ensuring that security is not sacrificed for convenience or functionality.
🔑 [CISO CERTIFICATION]
Discover How You Can Advance Your Career Through Cybersecurity
Show Notes:
1:00 - Introduction
2:00 - Measuring Security
5:00 - Cyber War
7:00 - Functionality vs. Security
14:00 - History of IT and Cybersecurity
18:00 - Challenges in Cybersecurity
22:00 - Security Sacrifices
About Dr. Eric Cole
Eric Cole, Ph.D., is an industry-recognized security expert with over 20 years of hands-on experience in consulting, training, and public speaking. As the founder and CEO of Secure Anchor Consulting, Dr. Cole focuses on helping customers prevent security breaches, detect network intrusions, and respond to advanced threats. In addition, he is a sought-after expert witness and a 2014 inductee to the Info Security Hall of Fame.
#WorldClassCISO #LifeOfACiso #LifeLessons #Lessons #CyberSecurity #InfoSec #CyberAware #DataProtection #Privacy #CyberThreats #ITSecurity #OnlineSafety #Hacking #DigitalSecurity #Trust #Identity #Personaltransformation #Mindset #CISO #CV #Challenge #CISOChallenge #LimitingBeliefs #Teamwork #growth #health #wellrounded #PodcastLife #PodcastJunkie #Podcasting #newpodcastalert #podcastseries #cybersecuritymetrics #metrics #cyberwar #war
Dr. Cole also explores the systemic issues within organizations that hinder effective cybersecurity. He points out the problematic structure where CISOs report to CIOs, who are primarily focused on availability and uptime, leading to conflicts of interest that compromise security. Dr. Cole advocates for a shift in responsibility and authority, urging companies to recognize that cybersecurity requires independent oversight and clear, measurable metrics that go beyond simply preventing visible attacks. He stresses the need for a fundamental change in how organizations approach cybersecurity, including holding decision-makers accountable for risks and ensuring that security is not sacrificed for convenience or functionality.
🔑 [CISO CERTIFICATION]
Discover How You Can Advance Your Career Through Cybersecurity
Show Notes:
1:00 - Introduction
2:00 - Measuring Security
5:00 - Cyber War
7:00 - Functionality vs. Security
14:00 - History of IT and Cybersecurity
18:00 - Challenges in Cybersecurity
22:00 - Security Sacrifices
About Dr. Eric Cole
Eric Cole, Ph.D., is an industry-recognized security expert with over 20 years of hands-on experience in consulting, training, and public speaking. As the founder and CEO of Secure Anchor Consulting, Dr. Cole focuses on helping customers prevent security breaches, detect network intrusions, and respond to advanced threats. In addition, he is a sought-after expert witness and a 2014 inductee to the Info Security Hall of Fame.
#WorldClassCISO #LifeOfACiso #LifeLessons #Lessons #CyberSecurity #InfoSec #CyberAware #DataProtection #Privacy #CyberThreats #ITSecurity #OnlineSafety #Hacking #DigitalSecurity #Trust #Identity #Personaltransformation #Mindset #CISO #CV #Challenge #CISOChallenge #LimitingBeliefs #Teamwork #growth #health #wellrounded #PodcastLife #PodcastJunkie #Podcasting #newpodcastalert #podcastseries #cybersecuritymetrics #metrics #cyberwar #war
Комментарии
 0:09:22
0:09:22
 0:36:24
0:36:24
 0:40:01
0:40:01
 0:01:42
0:01:42
 0:05:55
0:05:55
 0:31:38
0:31:38
 0:03:24
0:03:24
 0:02:14
0:02:14
 0:15:15
0:15:15
 1:01:07
1:01:07
 0:01:49
0:01:49
 1:07:38
1:07:38
 0:00:51
0:00:51
 0:01:47
0:01:47
 1:03:54
1:03:54
 0:46:02
0:46:02
 0:47:32
0:47:32
 0:06:03
0:06:03
 1:00:51
1:00:51
 0:04:25
0:04:25
 0:53:55
0:53:55
 0:24:25
0:24:25
 0:02:44
0:02:44
 0:06:18
0:06:18