filmov
tv
Building a Secure OT Network | SANS ICS Concepts

Показать описание
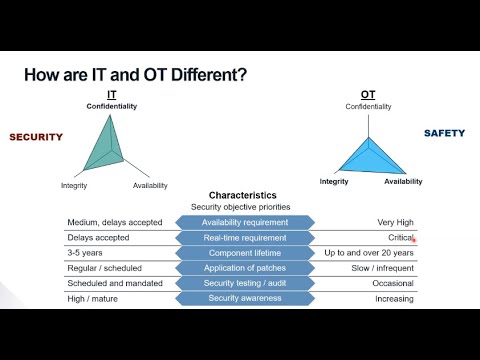
In this concept overview, we are joined by Don Brown Associate Director of Cyber Security at Verista. Don is here to discuss his experiences deploying a security OT network architectures. He walks us through a presentation that outlines his approach to achieving good zones and conduits to implement a reliable and secure operating environment.
If you enjoy this video, and the topics we cover in the SANS ICS concept overviews, be sure to like and subscribe to this channel. Leave a comment if you have a question about this topic or suggestions for future content.
References
Don C Weber's Social Media:
Don Brown's Social Media:
Verista's Social Media:
SANS ICS Training:
If you enjoy this video, and the topics we cover in the SANS ICS concept overviews, be sure to like and subscribe to this channel. Leave a comment if you have a question about this topic or suggestions for future content.
References
Don C Weber's Social Media:
Don Brown's Social Media:
Verista's Social Media:
SANS ICS Training:
Комментарии